BESS-Specialist Forensic Review
Independent BESS diagnostics and forensic review for serious asset decisions
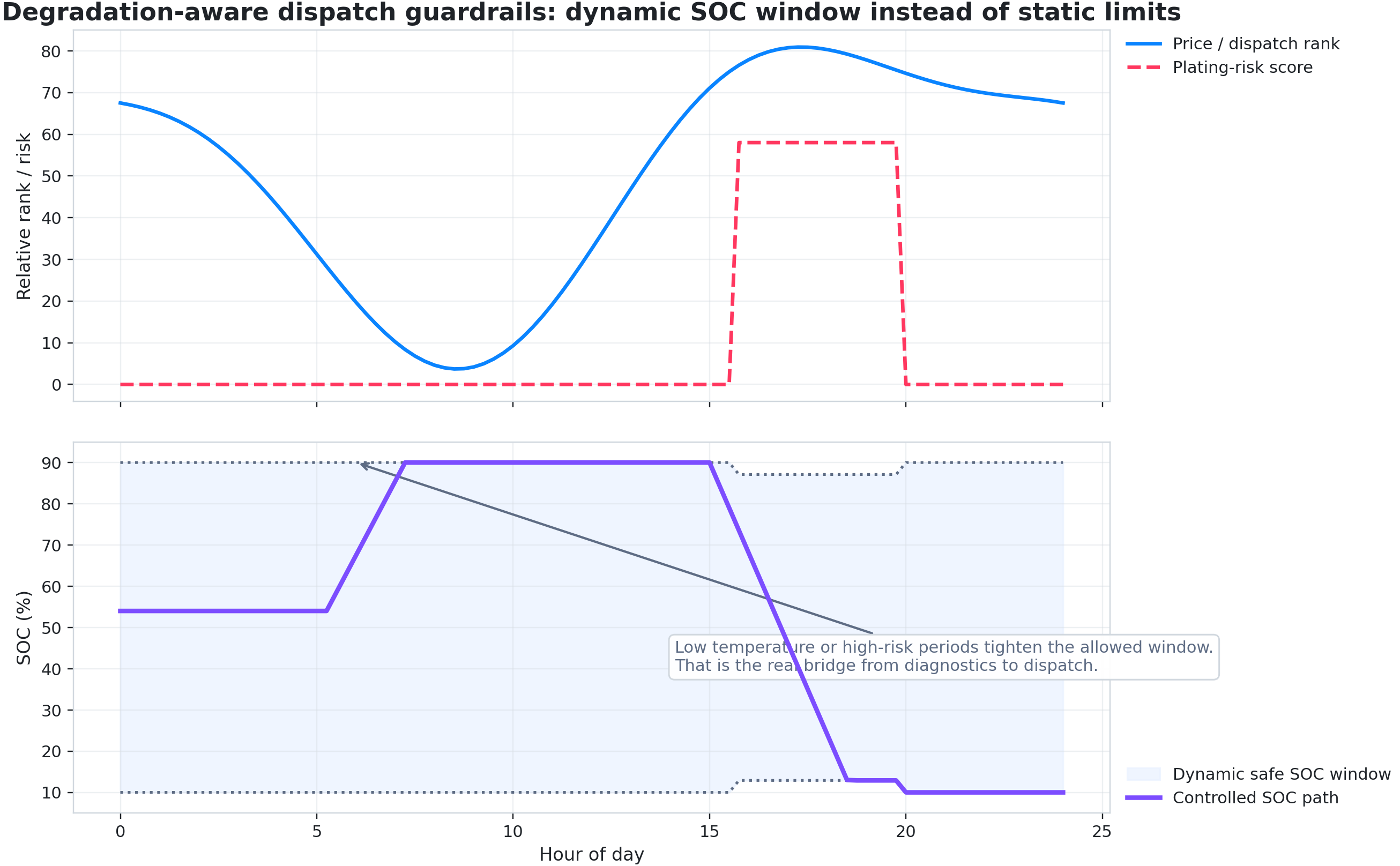
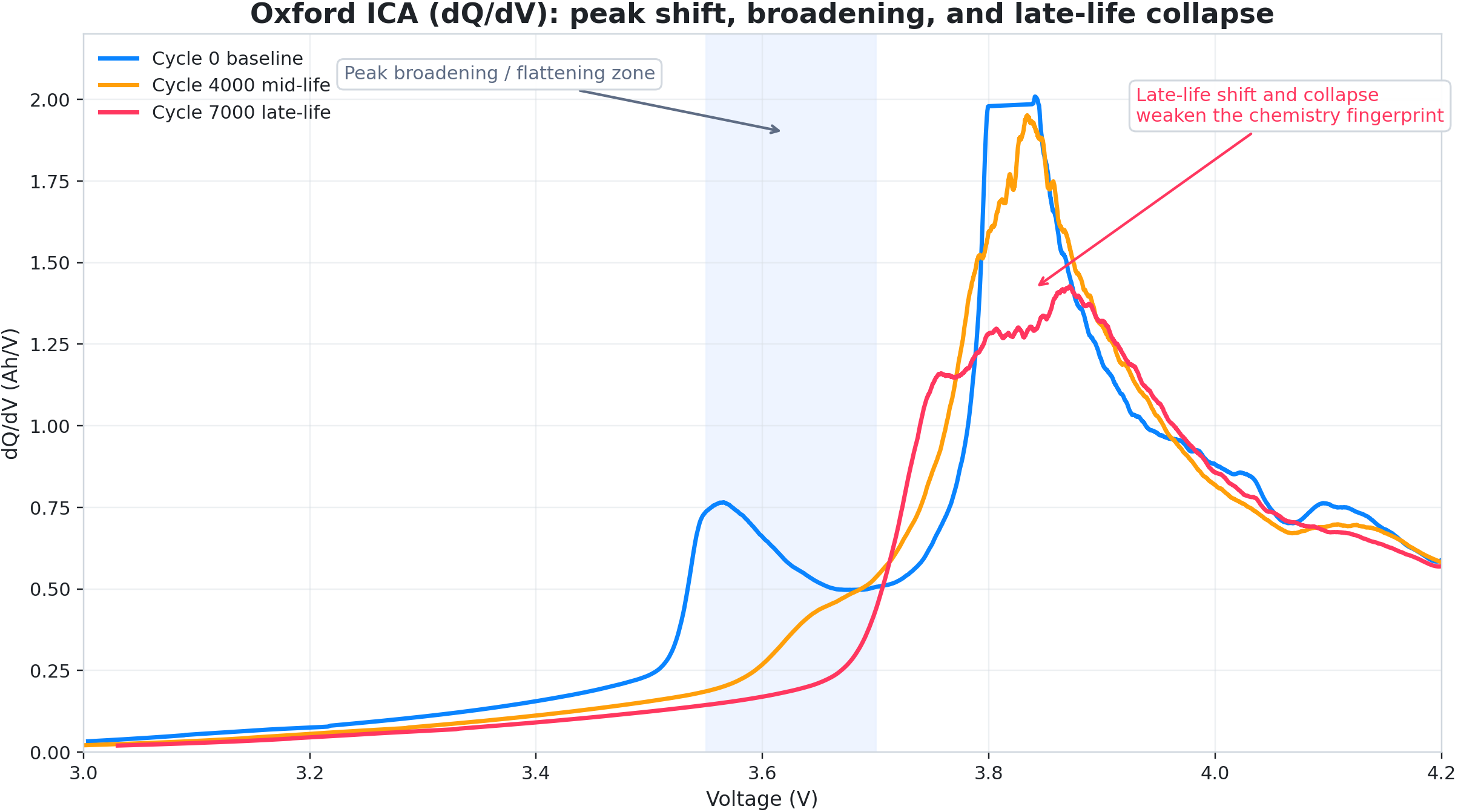
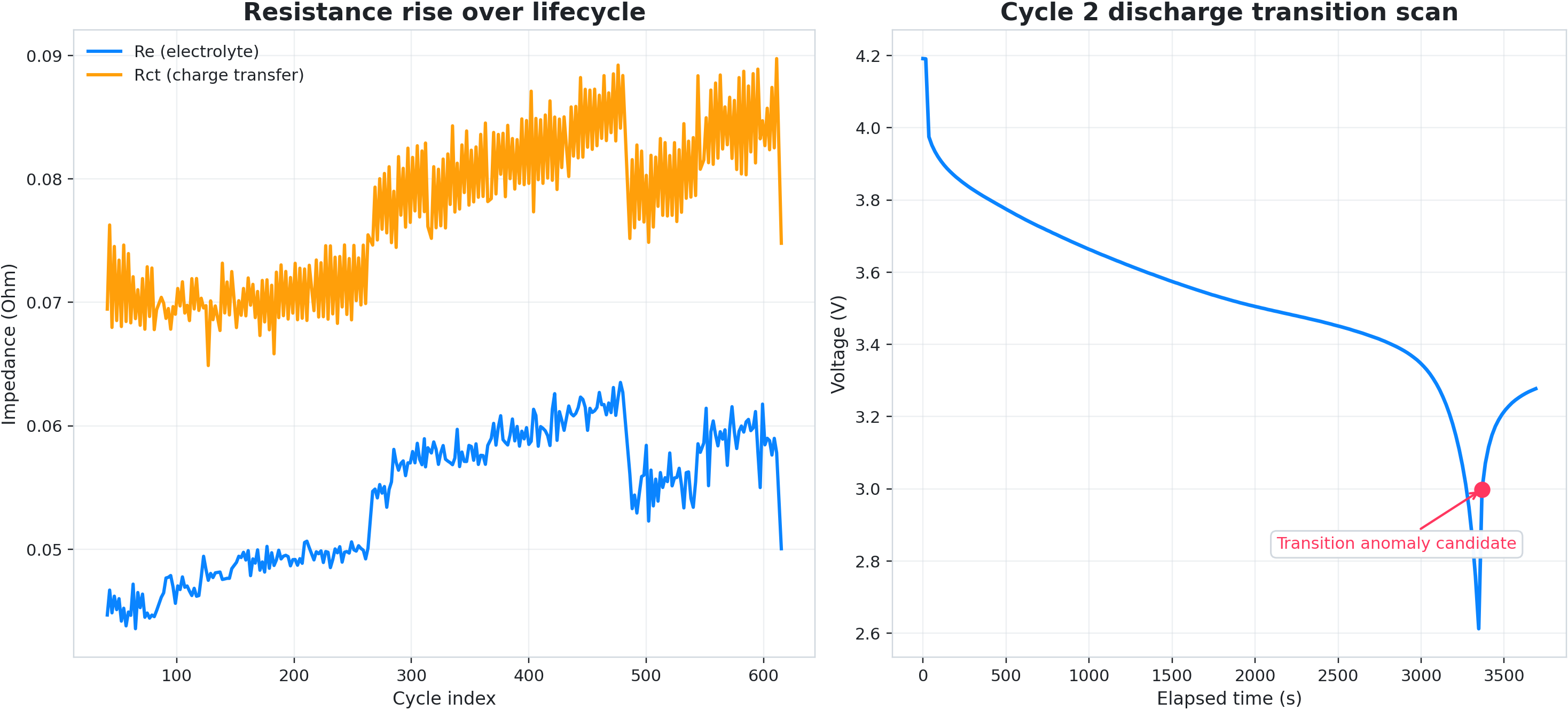
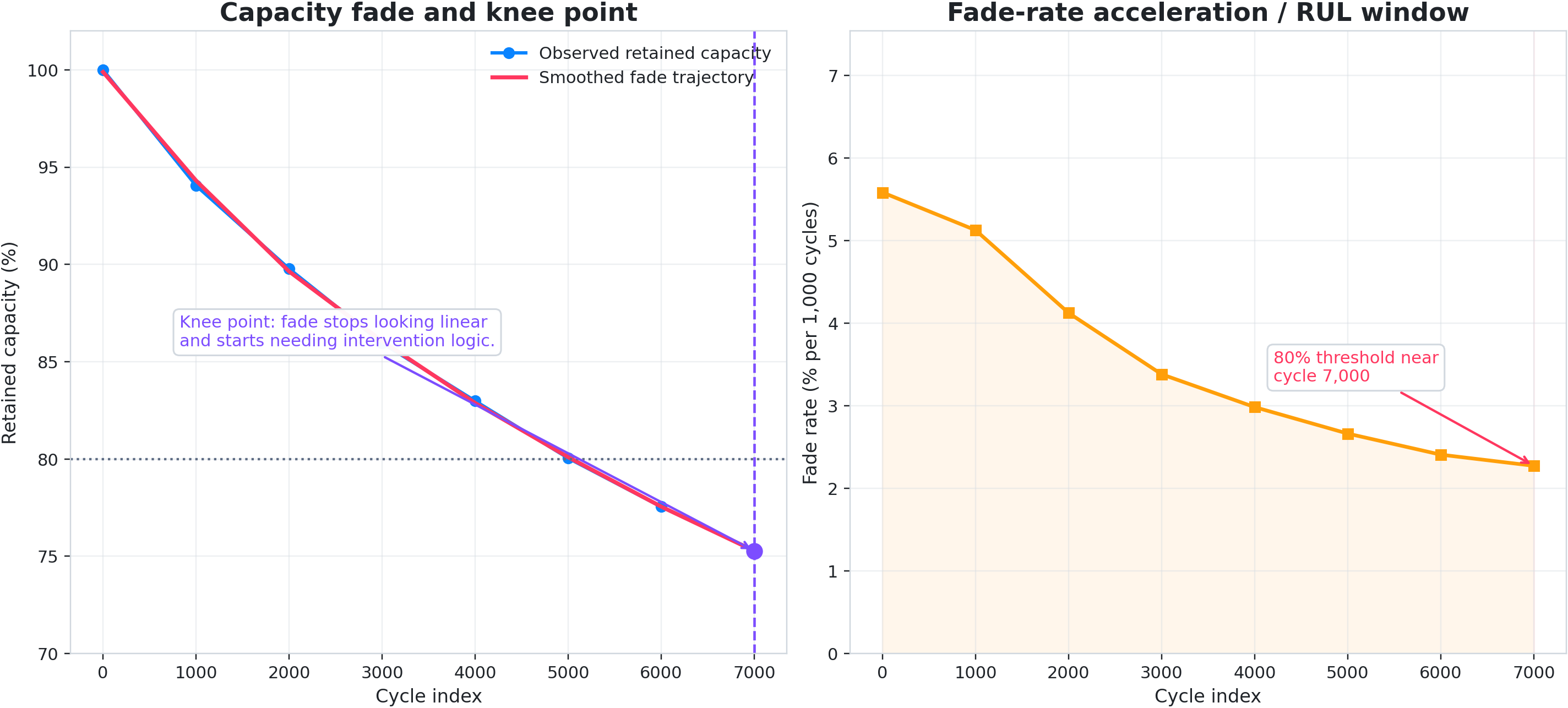
We review historical telemetry for investors, asset managers, and operating teams that need a clear answer quickly. Oxaide surfaces degradation, yield leakage, and failure patterns standard monitoring can miss, then returns a clear report in 5 business days.
Why BESS-first
Weak technical baselines get expensive quickly in storage. The same evidence can shape SPA terms, refinancing, warranty files, insurer review, and operating plans.
Send telemetry exports. We scope the review and return a clear report in 5 business days. Global execution, Singapore-headquartered.
5 business day reportFixed-scope entry pointUseable for diligence, warranty, or O&M
Best self-checkout fit: one bounded telemetry slice, one live decision, one fixed-fee answer. Broader mandates should go through direct review.